One thing you should never, ever do at the airport

Most of us would probably do this without a second thought.
You’ve been running around the airport all day, you have a three-hour wait for your connecting flight and your phone battery is running at 15 per cent.
One quick look around the food court of gate lounge and you’ll most like find an abundance of power points and USB ports to charge your device.
But it’s the USB ports you should definitely avoid.
Caleb Barlow, vice-president of X-Force Threat Intelligence at IBM Security, has revealed these charging stations can actually be tampered with by cybercriminals to install malware on your device or download all you info.
“Plugging into a public USB port is kind of like finding a toothbrush on the side of the road and deciding to stick it in your mouth. You have no idea where that thing has been,” Caleb told Forbes, saying the ports basically act like an open passageway from your device.
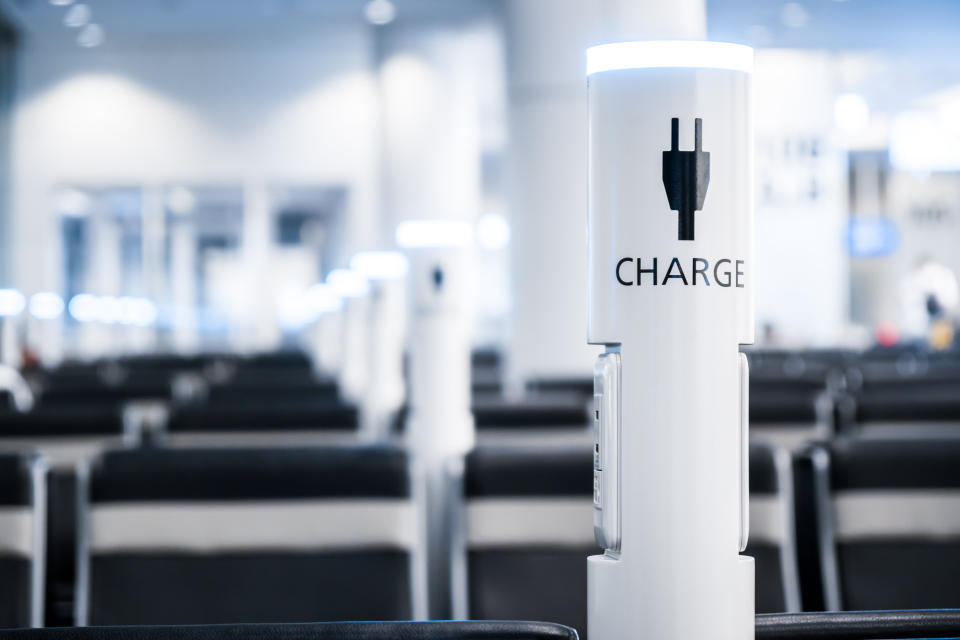
He also warns of using random tech accessories left behind by other travellers, like Apple charging cords for example.
“Let's say I’m a bad guy. I go into an airport. I’m not going to easily take apart the charging station but it’s easy just leave my cord behind,” he explained.
“Now, if you see an Apple charging cord, you're likely to grab it or just plug into it. But inside this cord is an extra chip that deploys the malware, so it charges your phone but now I own your computer.”

New research from the IBN X-FORCE survey revealed the transportation industry became the second-most attacked sector (after the financial sector) in 2018.
Since January of last year over 560 million records (and that’s just the publicly reported ones) from the travel and transportation industry have been leaked or compromised.
To save you the pain of getting hacked, Caleb suggests it’s much safer to bring your regular charger along and have it handy so you can plug it into a wall outlet.
Or get yourself a portable power bank to recharge your phone when you’re on the move.
Got a story tip? Send it to lifestyle.tips@verizonmedia.com
Want more lifestyle and celebrity news? Follow Yahoo Lifestyle on Facebook,Twitter and Instagram.
Or sign up to our daily newsletter here.