Sequoia backs Coana to help companies prioritise vulnerabilities using 'code aware' software analysis
Silicon Valley venture capital juggernaut Sequoia is backing a fledgling Danish startup to build a next-gen software composition analysis (SCA) tool, one that promises to help companies filter through the noise and identify vulnerabilities that are a genuine threat.
For context, most software contains at least some open source components, many of which are out-of-date and irregularly -- if at all -- maintained. This has led to all manner of security flaws, such as Log4Shell which impacted the open source Java logging framework Log4j and led to breaches impacting high-profile organisations such as a U.S. Federal agency which failed to patch the bug. In turn, this is leading to an array of fresh regulation, designed to strong-arm businesses into running a tighter software supply chain.
The problem is, with millions of components permeating the software supply chain, it's not always easy to know whether a given application is using a particular component. There are, of course, many software composition analysis (SCA) tools out there, from Snyk to Synopsis, which alert companies about known vulnerabilities in their technology stack -- but this can create a lot of noise, particularly if an application isn't actively using that component, thus making it difficult for security teams to prioritize the vulnerabilities that really matter.
And this is where Danish cybersecurity startup Coana is setting out to make a difference, using "code aware" SCA to help its users separate out irrelevant alerts and focus only on those that matter.
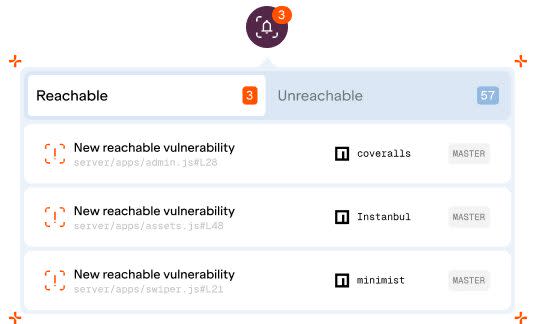
Coana: Example alerts
Founded out of Denmark in 2021, Coana is the handiwork of a computer science professor (Anders Møller) and two PhDs (Martin Torp and Benjamin Barslev Nielsen) who say they hit upon a "technical breakthrough" while part of a research group at Denmark's Aarhus University, discovering a new technique for analyzing and understanding large, JavaScript-based applications. CEO Anders Søndergaard joined the trio as co-founder in 2022, having exited a previous biometrics tech startup called Resilio the previous year.
To help fund their company through its early-access stage to full commercialization, Coana today announced it has raised $1.6 million in a pre-seed round of funding led by Sequoia Capital, with participation from Essence VC and a slew of angels including current and former executives from Google, Red Hat, and GitHub.
A typical application can consist of as much as 90% third-party libraries, the majority of which are open source and maintained (or not) by any number of volunteer developers.
So a company building software might build their own application layer that draws on these myriad libraries, creating a long chain of dependencies that are connected by functions. Traditionally, a SCA tool would look at the version number of a particular dependency, and map it against a database of known vulnerabilities and then report back to the developers if it finds a match. However, in many cases, an application might only use one or two functions from a library of maybe 50 -- so if a vulnerability exists in a part of the library that the app never calls, it shouldn't really impact that application.
Companies can use Coana to build what it calls a "call graph" of the entire application, spanning application code and dependencies, to understand the data flow paths, and then use that to eliminate false positives.
"The amount of packages being used and the lines of code can be extremely high volume, so it requires some really sophisticated static analysis," Søndergaard told TechCrunch. "The call graph enables us to do a huge analysis on all the possible paths between different dependencies. So imagine an application consisting of hundreds or thousands of dependencies, we can identify all the paths between those dependencies to understand which ones are truly vulnerable -- and which ones are not."
It is still very early days, of course, with Coana introducing the first iteration of its product in October for its first paying customers -- a mix of Series B and Series C-stage startups and scaleups. However, the company is working to expand its support beyond JavaScript and into Java and Python this year, which will help it target a broader customer base.
"As our product matures, and our company matures, we're moving up market, eventually targeting large enterprises, but that will take a while before we have the sophistication on the language support to get to get to that level," Søndergaard said.
Companies looking to check out Coana today can apply for early access now.

